You Got the Email. Now What?
WordPress just sent you a subject line you never want to see: "Your Site Is Experiencing a Technical Difficulty."
Your first instinct might be to forward it to your developer or close the tab and hope it resolves itself. Neither is the right move.
This email is WordPress's last-ditch attempt to tell you something broke at the PHP level — hard enough that the normal error display couldn't run. That distinction matters. A white screen or a generic 500 error usually means something went wrong during execution. This specific email means WordPress detected a fatal error and triggered its recovery mode — a feature introduced in WordPress 5.2 specifically to give site owners a path back in without locking them out entirely.
So yes, your site may still be partially functioning for visitors. But the admin dashboard is compromised, something is actively broken, and the longer you wait, the harder diagnosis becomes — especially if cron jobs start misfiring, transients go stale, or a second plugin update fires while the first conflict is still unresolved.
Let's fix it properly.
What the WordPress Critical Error Actually Means
The "technical difficulties" message doesn't mean your database exploded or your server is on fire. In most cases, it means one thing: a PHP fatal error killed the WordPress execution thread.
WordPress wraps its shutdown handling in a way that detects when a fatal error occurred. When it does, it emails the site admin with a secure recovery link, logs the error, and places the site into a protected mode. Visitors see a generic error message. You, as the admin, get a login-style recovery URL that bypasses the broken component.
The most common triggers — across the WordPress environments we work across regularly — are:
- A plugin update that introduced a PHP incompatibility. The plugin's new version requires PHP 8.1+ but your server is still on 7.4. The conflict surfaces the moment WordPress loads that plugin's bootstrap file.
- A theme function conflict. A functions.php edit — even a one-line addition — can create a fatal parse error that kills the entire request cycle.
- A plugin calling a deprecated or removed WordPress function. Plugin abandonment is a real risk. When a plugin hasn't been updated in 18+ months and you push a core WordPress update, you're running an untested, incompatible combination.
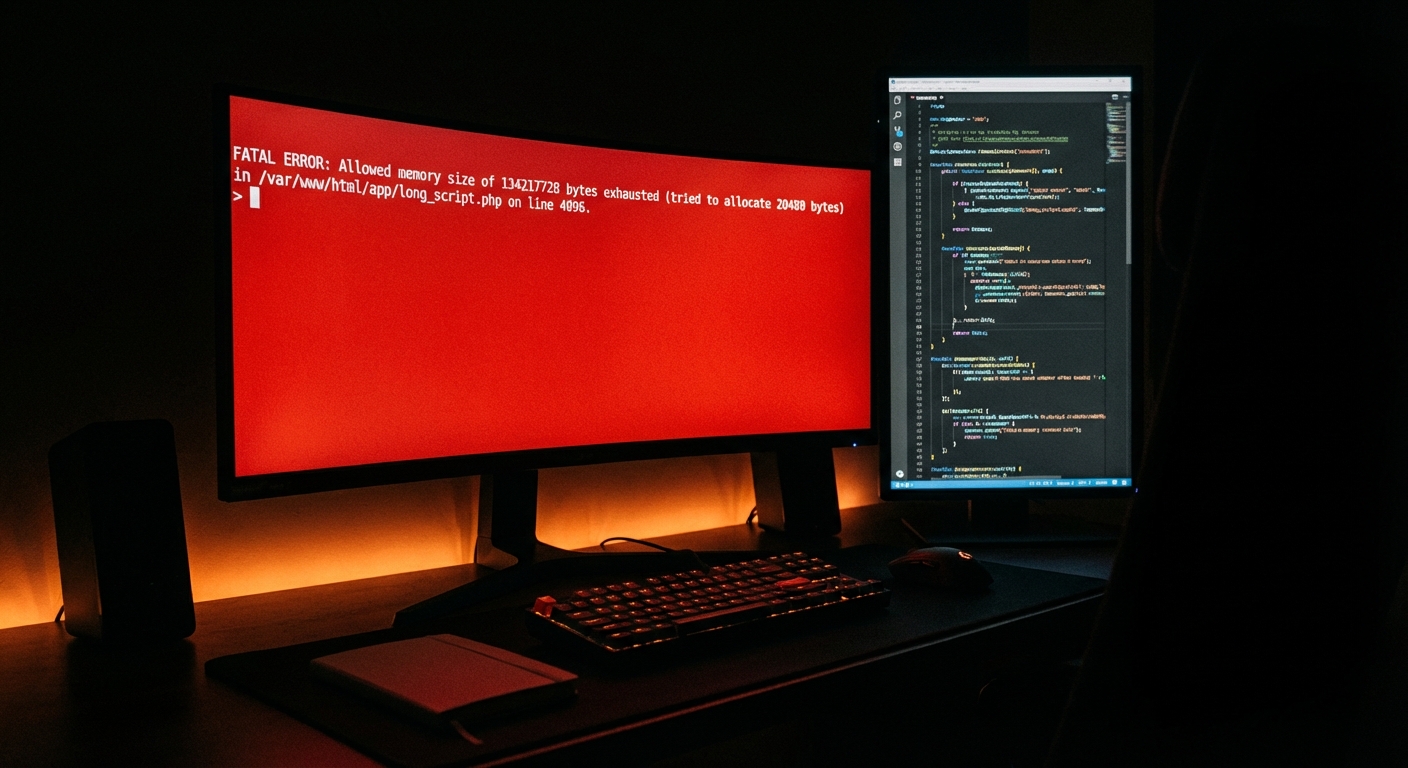
- Memory exhaustion. PHP's memory limit gets hit — usually because of an unoptimized query, a runaway loop, or an object holding too much in memory without proper cache invalidation through the object cache layer.
- Corrupt autoloaded data in
wp_options. Plugins that store excessive data in autoloaded rows can cause fatal memory overruns on page bootstrap, before any user-facing code even loads.
The error itself is always in the PHP error log, and WordPress writes it to wp-content/debug.log if you have WP_DEBUG_LOG enabled in wp-config.php. If you don't have debug logging active, you're already flying blind — and you were before this broke.
The Belief This Error Demolishes
Here's the default belief most WordPress site owners carry: "If my site has been running fine, my setup is fine."
That belief dies the moment you get this email.
Stability is not the same as health. A site can run for months with a plugin that hasn't been tested against current PHP versions, an outdated theme generating undocumented deprecation warnings buried in the error log, and a wp_options table bloated with tens of thousands of stale transients — and appear completely normal. Until it doesn't.
The critical error email doesn't signal a sudden catastrophe. It signals that a slow-building incompatibility finally crossed the failure threshold. The site was already fragile. The plugin update — or the server-side PHP version bump your host quietly pushed — was just the trigger.
That's the actual problem. Not the error message on screen. The underlying fragility that made the error inevitable.
Step-by-Step: How to Recover From the WordPress Critical Error
Step 1: Use the Recovery Mode Link
The email contains a unique, time-limited URL. Use it immediately — it bypasses the broken plugin or theme and grants you access to a restricted version of the admin dashboard. From inside recovery mode, you can deactivate the plugin or theme flagged in the error details.
Do not just clear the email and try logging in normally. You may not be able to, and you'll lose the contextual error information WordPress is surfacing right now.
Step 2: Read the Error — Literally
The email usually includes the exact error message. Read it. It will tell you:
- The file that caused the fatal error
- The line number within that file
- The error type: undefined function, class not found, allowed memory size exhausted, etc.
If you have SSH access, pull the actual PHP error log directly:
tail -n 50 /var/log/php_errors.log
Or check wp-content/debug.log. If that file doesn't exist, add the following to wp-config.php, reproduce the error, then read the output:
define('WP_DEBUG', true);
define('WP_DEBUG_LOG', true);
define('WP_DEBUG_DISPLAY', false);
Don't guess at the cause. The log exists. Use it.
Step 3: Deactivate the Offending Plugin or Theme via FTP or WP-CLI
If the recovery mode link has expired or went to spam, you have two reliable options:
Via FTP/SFTP: Navigate to wp-content/plugins/ and rename the folder of the suspected plugin (e.g., rename woocommerce to woocommerce_disabled). WordPress will auto-deactivate it on next load because the directory path no longer matches the registered plugin location.
Via WP-CLI (faster and more surgical if you have server access):
wp plugin deactivate plugin-name --skip-plugins --skip-themes
The --skip-plugins and --skip-themes flags are essential here. They prevent WordPress from loading any other plugins or the active theme during the command run — which means the deactivation executes even when the site is in a broken state. This is one of several scenarios where WP-CLI eliminates what would otherwise be a multi-step manual process.
If the issue is theme-side, switch to a default WordPress theme via WP-CLI:
wp theme activate twentytwentyfour --skip-plugins --skip-themes
Step 4: Verify PHP Version Compatibility
Once the immediate error resolves, confirm what PHP version your server is running:
wp --info
Cross-reference that output against the failing plugin's WordPress.org listing and changelog. Check the "Requires PHP" field. If the plugin requires PHP 8.0+ and you're on 7.4, or vice versa — you've found the structural incompatibility. Simply reactivating the plugin without addressing this will reproduce the same error.
Also flag any plugin that hasn't received an update in 12+ months. Plugin abandonment risk is underestimated. An unmaintained plugin running on current WordPress core versions is a fault waiting to surface.
Step 5: Confirm Your Rollback Position
Before making further changes — updating PHP, swapping plugins, editing functions.php — confirm you have a verified backup and a working rollback strategy.
A proper rollback strategy means:
- A full-site backup (files + database) captured before the last update cycle that triggered this error
- The ability to restore that backup in minutes, not hours
- A staging workflow where every plugin, theme, and core update is tested in isolation before touching production
If no pre-error backup exists, proceed carefully and test every change individually. You're recovering without a safety net at this point.
Step 6: Run a Post-Recovery Audit
Once the site loads again, don't stop at the visible fix. The fatal error was just the loudest signal. Other signals are quieter.
Check:
wp_optionsautoloaded data — run a size audit on autoloaded rows. Bloated autoload can destabilize object cache behavior and slow page bootstrap before a single template loads.- Cron jobs — run
wp cron event listto check for misfired or backed-up scheduled events. Downtime windows often leave cron queues in disarray. - PHP error log — look for non-fatal warnings and deprecation notices that indicate future breakage points.
- Plugin list — identify any plugin with no updates in the past year. Log them as risk items and evaluate whether maintained alternatives exist.
- Query Monitor diagnostics — if you're not already running Query Monitor on a staging environment, it's worth installing to surface slow queries and hook load issues that compound under scale.
A fatal error recovery is an audit trigger. Treat it as one.
Why This Keeps Happening (And Why Manual Fixes Don't Scale)
If this isn't your first WordPress critical error, the problem isn't the plugins. The problem is the absence of a maintenance system.
Proactive WordPress maintenance — real maintenance, not clicking "Update All" once a month and hoping — involves:
- Monitoring PHP error logs continuously, not after a site breaks
- Running updates through a staging workflow before they hit production
- Tracking plugin abandonment risk before a developer stops maintaining their code
- Auditing
wp_optionsautoload size before it becomes a performance and stability liability - Maintaining a tested rollback on every deployment, not scrambling for one after the fact
Manual updates without a system aren't maintenance. They're repeated exposure to the same risk.
For a WooCommerce store averaging $4,000/day in revenue, downtime costs roughly $166/hour. A two-hour recovery window — which is optimistic if you don't have WP-CLI access, error log visibility, or an on-call developer — costs more than a full year of professional maintenance plans for most business tiers.
If you want to understand what a structured maintenance approach actually includes, explore what's covered in a managed WordPress care plan — including update management, rollback protocols, and continuous monitoring.
What a Maintained Site Looks Like
A properly maintained WordPress site doesn't generate surprise critical error emails. The structural difference:
Update protocol: Every core, plugin, and theme update runs through staging first. If it breaks staging, it never reaches production. Rollback is confirmed before every deployment.
PHP compatibility tracking: Plugin and theme PHP requirements are tracked before any server-side PHP version change — including changes quietly pushed by managed hosts.
Log monitoring: PHP error logs and WordPress debug logs are monitored continuously. Non-fatal warnings get triaged before they graduate to fatal errors.
wp_options hygiene: Autoloaded data is audited on a cadence. Stale transients are purged. Object cache behavior is verified after major update cycles.
Cron reliability: WordPress cron job health is monitored. On high-traffic or WooCommerce sites, a system-level cron replaces WP-Cron entirely for reliability.
None of this is complex. It's operational discipline applied consistently. Most WordPress sites don't have it — and most site owners discover that only after an incident like this one.
For a full breakdown of what this looks like in practice, the Vimsy WordPress maintenance checklist covers the complete audit and operational structure we apply across site care engagements.
If You Can't Resolve It — Get Professional Help
Not every site owner has SSH access, WP-CLI installed, or the time to read PHP logs during a business emergency. That's a legitimate constraint.
If the site is still down, if the error log points to something you can't diagnose, or if you've run through the steps above without resolution — stop guessing. Blind troubleshooting on a broken production site, especially one processing live orders, creates compounding problems and extends downtime.
Vimsy's emergency WordPress support is built specifically for this: production sites that need fast, experienced diagnosis and recovery without the trial-and-error.
For site owners who want to stop reacting and start preventing, review our maintenance plans and pricing — and understand what ongoing protection actually costs versus what reactive recovery typically runs.
The Bottom Line
The critical error email is not the problem. It's the symptom of a site that was never structured to prevent this class of failure.
Fix the immediate error using the steps above. Then do the post-recovery audit. Then decide whether you want to keep operating reactively — one emergency at a time — or build a system that catches these things before they reach production.
Look — I'm writing this because this is a problem I see constantly, and it's also exactly what we built Vimsy to solve. If you want professionals handling this instead of hoping nothing breaks, book a free call.
A site that sends you critical error emails isn't just inconvenient. It's telling you the foundation needs attention. That message is worth listening to.