WordPress Spam Is a Performance Problem — Not Just an Inbox Problem
Spam is the maintenance task that feels low-stakes until it isn't. It doesn't break your site in a single event — it degrades it steadily, across multiple layers, in ways that don't show up on a status page or a speed test. By the time most site owners recognize the scope, the cost is already running.
Across dozens of WordPress audits, the pattern is consistent: sites that haven't actively managed spam have bloated comment tables, polluted transient caches, and contact forms generating thousands of junk submissions per month. The site looks fine on the surface. Under the hood, it's carrying weight it doesn't need to.
This guide covers what WordPress spam comments, fake form submissions, and registration spam actually do to your installation — and how to build a layered defense that stops them without damaging legitimate conversions.
Why Spam Hits WordPress at Scale
Spambots target WordPress installations because the architecture is predictable. Comment endpoints, registration forms, and contact form structures are standardized across millions of sites. Bots don't attack your site specifically — they run automated crawlers that identify WordPress by fingerprint and fire submissions in bulk.
When you talk about how to stop spam on WordPress, you're actually talking about three separate problems:
WordPress spam comments fill wp_comments and wp_commentmeta with junk rows. At volume, this degrades comment query performance, inflates backup sizes, and — if your theme queries recent comments — adds measurable overhead to page rendering.
WordPress spam forms — fake submissions to your contact forms — hit your inbox, your CRM, and your notification pipeline. But depending on which form plugin handles the submission, that data can also write directly to the database, sometimes as transients in wp_options.
Registration spam builds fake subscriber accounts in wp_usermeta. At scale, it bloats your user table, corrupts marketing data, and — if role assignment logic has any gaps — creates low-level security exposure.
None of these fail loudly. They accumulate quietly, and start costing you in processing overhead, storage, email deliverability, and developer time.
The wp_options Problem Nobody Talks About
Here's the part that gets skipped in most spam discussions. Some form plugins — including popular ones — store submission records and session data as transients in wp_options. Transients are designed to be temporary cache entries, but when spam floods a form, they pile up faster than WordPress's garbage collection can clear them.
Run this in WP-CLI on a neglected site:
wp db query "SELECT COUNT(*) FROM wp_options WHERE option_name LIKE '_transient_%'"
On a site that's been absorbing WordPress form spam without controls, that number can reach tens of thousands. The problem: WordPress loads all autoloaded options into memory on every request — including expired transients that haven't been cleaned. That's database overhead on every page load, caused entirely by uncontrolled form submissions.
This is exactly the kind of hidden cost that surfaces in a full WordPress site audit but never appears in an uptime dashboard.
The Belief That's Costing You: "Spam Is Just an Inbox Problem"
Most site owners treat spam as a moderation inconvenience — something to batch-delete when the inbox gets bad enough. That framing drives the wrong response: periodic cleanup instead of systematic prevention.
The actual cost breakdown:
- Database bloat from
wp_commentsandwp_optionsgrowth slows query performance site-wide - Email deliverability damage when spam submissions trigger high-volume outbound notifications — your sender reputation degrades, and eventually legitimate transactional emails start landing in spam folders
- Storage overhead carried on every backup cycle against a table padded with hundreds of thousands of junk rows
- Operational blind spots — at high enough spam volume, inbox monitoring becomes unreliable. You stop noticing real submissions buried in the noise.
That last one is underrated. WordPress spam forms don't just waste inbox space — they reduce your ability to detect legitimate contact attempts, qualified leads, or — in the worst case — genuine security alerts embedded in form notifications.
Layer 1: Akismet WordPress — The Baseline, Not the Full Solution
Akismet is the right starting point for managing WordPress spam comments. It filters submissions against a continuously updated global database of known spam patterns, catches most junk before it reaches your moderation queue, and runs server-side with no frontend performance cost.
But treat it as a foundation, not a ceiling.
Akismet is reactive. It catches known patterns. Novel spam vectors take time to propagate through its model. More importantly: Akismet doesn't block bots from submitting — it filters after the fact. At high volume, every blocked comment still triggers a database write and a server process. That processing cost compounds.
For forms: Akismet only integrates with contact forms if your form plugin explicitly supports it. By default, Akismet protects WordPress spam comments. Nothing else. Form spam requires separate controls.
Layer 2: Honeypot Fields — Invisible to Users, Lethal to Bots
A honeypot is a hidden form field — invisible in the rendered browser output, present in the HTML. Real users never fill it in. Bots that blindly populate all fields do. When that hidden field arrives populated in the submission, you reject it silently.
No WordPress CAPTCHA friction. No API dependency. No JavaScript requirement. Zero false positives from real users.
In most audits we perform on sites struggling to stop spam on WordPress, a missing or disabled honeypot on the contact form is the single most common gap. Gravity Forms, WPForms, and Fluent Forms all include honeypot support — it just needs to be enabled.
Honest caveat: sophisticated bots can detect CSS-hidden fields by checking computed styles. Honeypots stop the majority of automated traffic — they don't stop a targeted, intelligent attacker. As the first line of defense in a layered stack, they eliminate the bulk of volume with zero user experience cost.
Layer 3: WordPress CAPTCHA — Match Friction to Risk
WordPress CAPTCHA implementations range from invisible to mildly annoying to legitimately conversion-damaging. The right choice depends on the form, the traffic, and the threat level.
The main options:
reCAPTCHA v3 (Invisible) assigns a behavioral risk score with no user interaction. Lowest friction — but threshold tuning requires active monitoring, or you'll generate false positives on real users. Also routes behavioral data to Google, which matters for GDPR-sensitive audiences.
reCAPTCHA v2 (Checkbox) requires the "I'm not a robot" click. Medium friction. Effective and widely deployed.
hCaptcha is the privacy-respecting alternative — comparable UX to v2, no Google data dependency. A better default for EU-based sites.
Cloudflare Turnstile operates invisibly and independently of Google. If your site already runs behind Cloudflare, evaluate this first.
Math/logic CAPTCHAs — low friction, adequate for low-risk forms. Easy for sophisticated bots to defeat, but they add a useful layer in combination with other methods.
The principle: match protection to actual risk. A low-traffic service business contact form doesn't need the same WordPress CAPTCHA configuration as a WooCommerce account registration form being hit by credential-stuffing bots. Over-protecting low-stakes forms costs legitimate conversions. Under-protecting high-stakes forms costs real money.
Our WordPress care plans include configuration reviews for this setup — because a misconfigured CAPTCHA can cost you leads while leaving spam largely unaffected.
Layer 4: Hardening the Comment System
If comments aren't part of your site's actual value, disable them globally and eliminate the attack surface entirely.
Via WP-CLI, close comments on all existing posts at once:
wp post list --status=publish --format=ids | xargs wp post update --comment_status=closed
If comments matter to your site, tighten the defaults:
- Require user registration to comment. Eliminates anonymous bot submissions immediately.
- Hold all first-time comments for moderation. Removes the incentive for bots targeting public visibility.
- Set link-count thresholds for automatic moderation. WordPress can queue any comment with more than N links — bots love link drops.
- Block XML-RPC. XML-RPC is a legacy remote publishing endpoint that bots regularly exploit for WordPress spam comment injection. Modern WordPress uses the REST API for remote publishing. XML-RPC is unnecessary. Block it in
.htaccess:
<Files xmlrpc.php>
Order Deny,Allow
Deny from all
</Files>
This .htaccess hardening adds no performance overhead and removes a persistent, well-documented attack vector.
Layer 5: Registration Spam
Membership sites, LMS platforms, and WooCommerce stores with account creation face a distinct spam problem. Bots register fake accounts to probe for privilege escalation, seed marketing automation with junk data, and build user lists for future spam campaigns.
Controls that hold up:
Email verification on registration is the most effective single countermeasure. Most bots use disposable addresses that can't complete a verification loop. This step alone blocks the majority of fake account creation.
WordPress CAPTCHA on the registration form adds a second barrier for bots with valid email access.
Disposable domain blocking — block known throwaway email providers (mailinator, tempmail, guerrillamail) at the form validation layer. A simple domain blocklist at registration kills a significant share of junk accounts before they're created.
WP-CLI subscriber audits — track subscriber accumulation against known user acquisition rates:
wp user list --role=subscriber --format=count
If that count grows faster than your actual signups, registration spam is active. Catching it early prevents it from becoming a database indexing problem on the users table at scale.
The Full Stack
No single tool covers everything. The right approach stacks layers:
| Layer | Tool | Coverage | |---|---|---| | WordPress spam comments | Akismet | Reactive pattern filtering | | All forms | Honeypot fields | Silent bot deterrence | | High-risk forms | reCAPTCHA v3 or hCaptcha | Active behavioral verification | | Comment system | WP-CLI disable + moderation settings | Attack surface elimination | | XML-RPC | .htaccess rule | Legacy endpoint blocking | | Registration | Email verification + domain blocking | Fake account prevention | | Database | WP-CLI transient cleanup | wp_options bloat removal | | Network layer | Cloudflare or Wordfence WAF | Bot blocking before WordPress loads |
The WAF layer deserves emphasis. A network-level firewall blocks repeat bot IPs at the edge — before they trigger a WordPress process at all. This is especially valuable once bots have already found your comment or registration endpoint and are running sustained campaigns.
For a full review of where your current setup has gaps, the Vimsy WordPress maintenance checklist covers the audit scope we use on every onboarding.
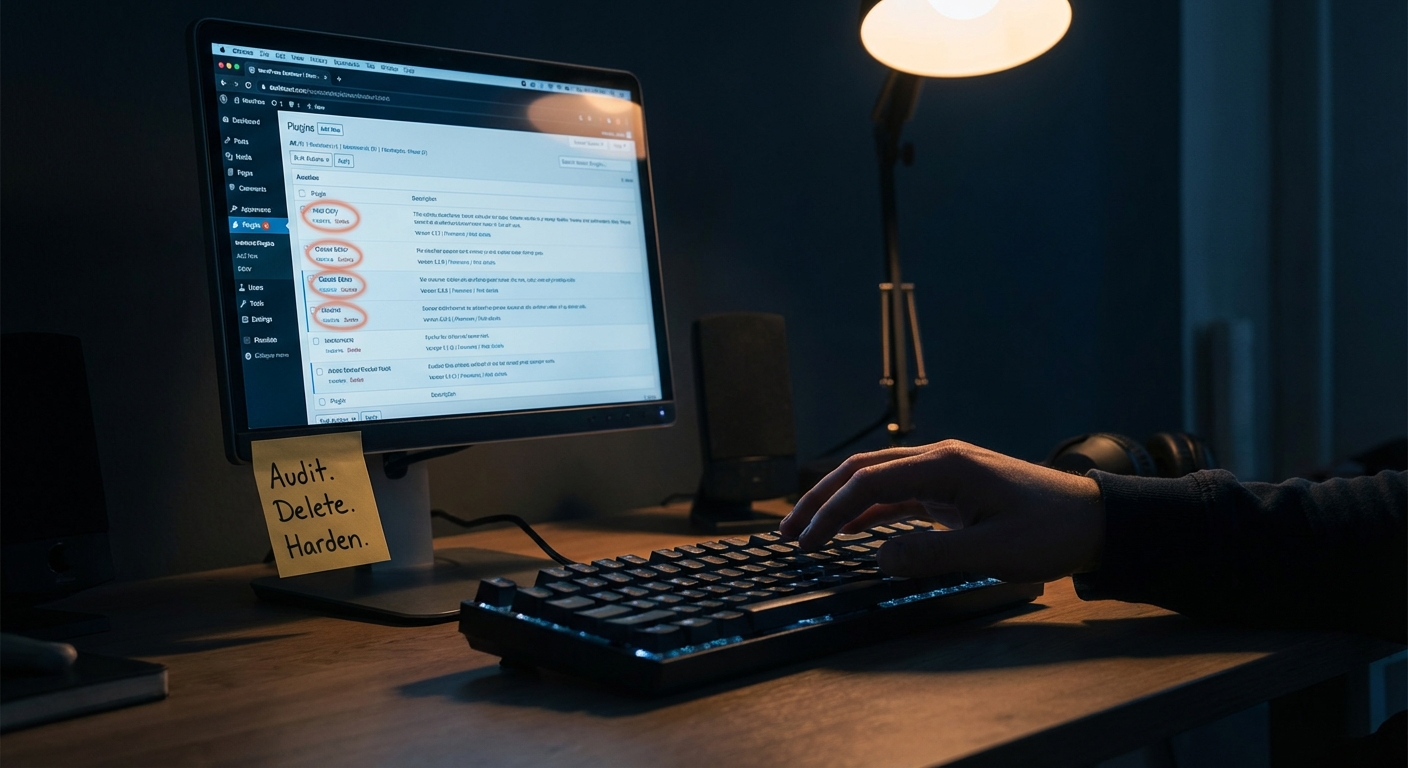
This Is a System, Not a Configuration
The biggest failure mode isn't choosing the wrong CAPTCHA library. It's treating spam defense as a one-time setup.
Spam tactics evolve. Honeypot patterns get fingerprinted by new bot variants. reCAPTCHA threshold scores drift over time. Akismet requires an active API key and a current plugin version to function properly.
PHP version compatibility matters here too. Several anti-spam plugins have quietly dropped support for PHP 7.x. Running outdated PHP isn't just a generic security risk — it can silently disable the specific layers protecting your comment and form endpoints. An anti-spam plugin that fails gracefully on an incompatible PHP version gives you false confidence while leaving you exposed.
In most audits we perform on sites reporting active spam problems, at least one protection layer is either misconfigured, outdated, or running on an incompatible PHP version. The site owner believes they're protected. The logs say otherwise.
That's not maintenance. That's assumption management.
The Actual Operational Cost
Pull up a neglected WordPress install. Run a database diagnostic. Check the wp_comments row count. Run the transient query above. Check the wp_options autoload size. These are concrete numbers — and in most cases, they tell a story the uptime monitor will never surface.
WordPress spam comment and form spam bloat doesn't create a 503 error. It creates a 2-second query that compounds across every page load. It degrades deliverability on transactional emails. It buries legitimate form submissions under noise until someone stops checking.
For any site where contact form conversions matter — even a small service business taking in a handful of qualified inquiries per week — missing one real lead because it was lost inside a spam flood is a cost that far exceeds the effort required to implement proper controls.
Build the system. Then maintain it as part of a regular WordPress site maintenance routine.
Look — I'm writing this because this is a problem I see constantly, and it's also exactly what we built Vimsy to solve. If you want professionals handling this instead of hoping nothing breaks, book a free call.
Spam is boring until it isn't. By the time it becomes urgent, you've already paid for the neglect.