WordPress Multisite Looks Like a Shortcut. It Isn't.
Running multiple WordPress sites and managing each one separately is genuinely painful. WordPress Multisite exists to solve that. One installation, one dashboard, one set of core files — and every site in your network shares the infrastructure. On paper, it sounds like the obvious choice for agencies, franchise businesses, and SaaS operators running dozens of properties.
In practice, it's a different conversation.
Multisite doesn't reduce complexity — it relocates it. What you gain in centralized control, you pay for in architectural constraints, maintenance overhead, and a failure surface area that spans every site in the network simultaneously.
What WordPress Multisite Actually Is
At its core, WordPress Multisite converts a single WordPress installation into a network of sites, all sharing the same codebase, the same wp-config.php, and the same database — with site-specific data stored in separate table prefixes (e.g., wp_2_posts, wp_3_options).
This matters for several reasons:
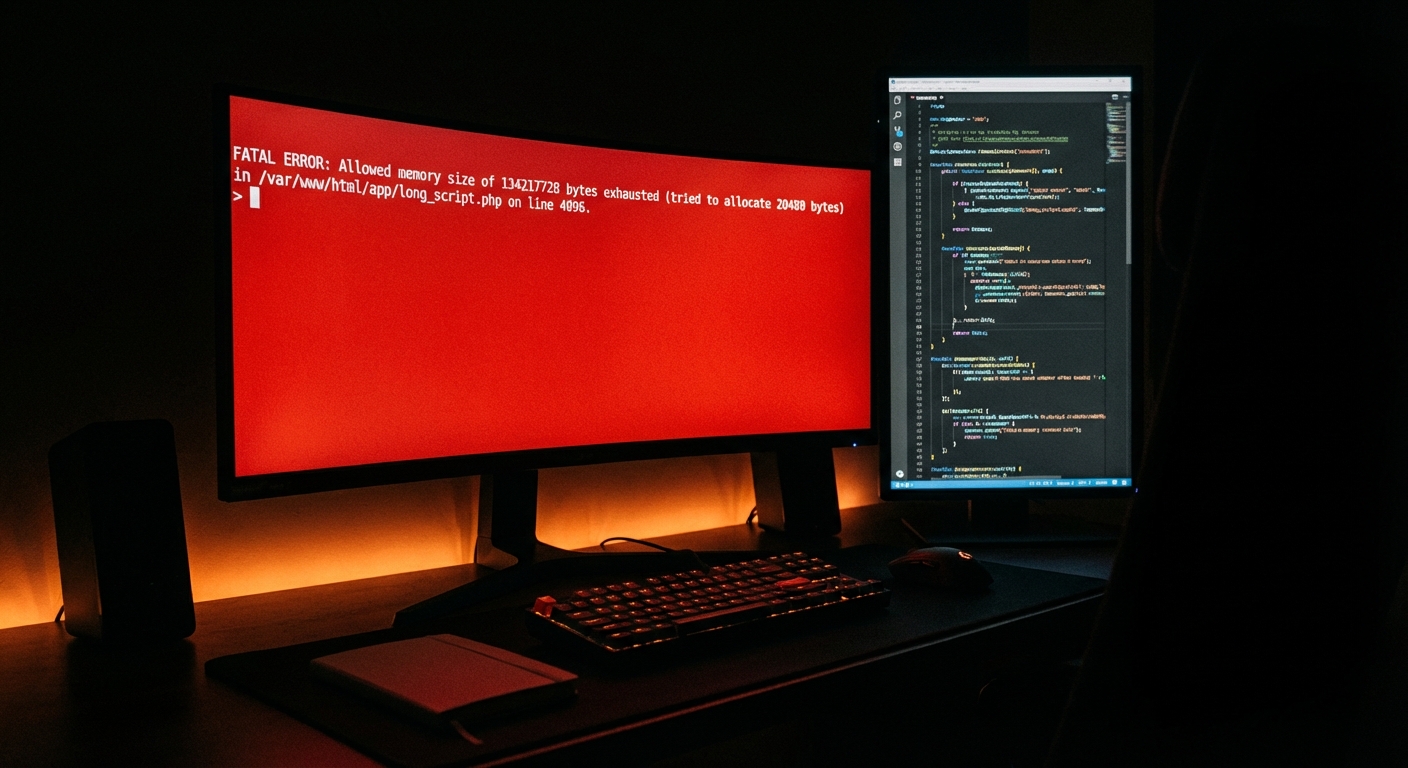
One codebase, one point of failure. A PHP compatibility issue, a bad plugin update, or a corrupted wp-config.php can take every site in the network down — not just one.
Shared plugin and theme infrastructure. Plugins are network-activated or site-activated, but they're installed at the network level. You can't run different plugin versions for different subsites. If Site A needs Plugin X at version 3.2 and Site B needs it at version 4.0, you have a conflict with no clean resolution inside Multisite.
The wp_options table behaves differently. Each subsite gets its own options table (e.g., wp_3_options), but network-wide settings live in wp_sitemeta. Autoloaded data from every subsite contributes to memory pressure. In large networks, this gets ugly fast — especially when plugins aren't written with Multisite in mind and start dumping data indiscriminately.
User roles operate at two levels. Super Admins control the network. Site Admins control individual sites. Misconfiguring this — which happens more than it should — creates either security holes or frustrated clients who can't manage their own content.
When Multisite Makes Sense
Don't let the complexity warnings above scare you away from Multisite entirely. There are scenarios where it's genuinely the right architecture.
Franchise and regional business networks. If you're managing 30 locations for a single brand — same theme, same functionality, different content — Multisite is purpose-built for this. One core update propagates across the network. Branding stays consistent. Regional managers get access to their subsite without touching others.
University or enterprise intranets. Departmental microsites under a single domain (e.g., marketing.university.edu, engineering.university.edu) are a textbook Multisite use case. Shared authentication, shared infrastructure, isolated content management.
SaaS platforms with site-per-user architecture. Some SaaS tools provision a WordPress subsite per customer. If your product requires WordPress as the delivery layer, Multisite can be a reasonable infrastructure choice — though it comes with serious caveats around scaling, object cache configuration, and cron job management across hundreds of subsites.
The pattern that emerges across these cases: the sites share far more than they differ. Same theme. Same plugins. Same base functionality. The content is different; the machinery is identical. That's when Multisite earns its place.
If your sites need different plugins, different themes, different PHP configurations, or different server environments — Multisite will fight you at every turn. Separate installs with a shared management layer (like MainWP or WP-CLI scripting) will serve you better.
The Setup Reality Nobody Talks About
Setting up WordPress Multisite isn't technically difficult. You add define('MULTISITE', true); and a handful of constants to wp-config.php, choose between subdomain and subdirectory structure, update your .htaccess rewrite rules, and you're running a network.
The hard part isn't activation. It's everything that follows.
Subdomain vs. subdirectory. This decision is permanent without a migration. Subdomains (site1.yourdomain.com) require wildcard DNS configuration. Subdirectories (yourdomain.com/site1) are simpler but create URL dependency on the root domain. Choose based on your long-term architecture, not what's easiest today.
SSL configuration. In a subdomain setup, you'll need a wildcard SSL certificate. Let's Encrypt supports this, but renewal automation requires DNS challenge validation — which adds operational overhead most teams don't account for upfront.
Object caching at network scale. Without a proper object cache layer — Redis or Memcached configured at the server level — a large Multisite network hammers the database on every request. Transients stored in the database compound this. At 20+ subsites with moderate traffic, uncached Multisite becomes a performance liability.
Staging workflows become non-trivial. You can't simply clone a subsite to staging. You're cloning the entire network or maintaining a separate staging network. Most teams realize this after the fact, which is when staging discipline tends to collapse entirely.
Plugin compatibility is a real filter. Not all plugins are Multisite-compatible. Some write data to wp_options without respecting the subsite context, polluting network-level data. Others simply don't work correctly when network-activated. Before building a Multisite network around a plugin ecosystem, audit compatibility explicitly — not by reading the plugin page, but by testing in a network environment.
Maintenance on Multisite: The Risk Multiplier
Here's where most teams underestimate Multisite. Maintenance isn't harder in a linear way — it's harder in an exponential way.
In a standard WordPress install, a failed plugin update breaks one site. You roll back via WP-CLI (wp plugin update with --dry-run, then rollback if needed), restore from backup, diagnose. Problem contained.
In a Multisite network, a failed core update or incompatible plugin at the network level breaks every subsite simultaneously. Your rollback strategy needs to account for the entire network, not a single install. Backups need to capture both the shared tables (wp_users, wp_usermeta, wp_site, wp_blogs, wp_sitemeta) and the per-site tables. If you're not running automated backups with restore testing, this is a catastrophic risk sitting in your infrastructure.
Database bloat accumulates faster. Every subsite generates its own wp_X_options autoloaded data, its own post revisions, its own transients. Across a 20-site network, unmanaged database growth is significant. Without scheduled cleanup — expired transients, post revision limits, orphaned metadata — query performance degrades across the entire network.
Cron jobs multiply. WordPress runs pseudo-cron via wp-cron.php. In a Multisite network, cron runs per-site. With 30 subsites, you have 30 independent cron queues, each capable of failing silently. Missed scheduled posts, failed email deliveries, broken WooCommerce order processing — all traceable to cron failures that nobody noticed until something broke. Replacing WP-Cron with system cron via WP-CLI is non-negotiable at network scale.
Security incidents span the network. A compromised plugin that gets network-activated immediately has access to every subsite. Malware injections in a Multisite environment require full-network scanning and remediation — not just isolating a single install. REST API exposure becomes a wider attack surface when it spans dozens of subsites under a shared authentication system.
Query Monitor diagnostics in Multisite reveal problems that don't show up on single-site installs — cross-site queries, network table joins, plugin conflicts that only surface when network-activated. Most teams don't run Query Monitor at all, which means these problems accumulate invisibly.
The Honest Trade-Off Calculation
Multisite makes operational sense when:
- Your sites are architecturally identical
- Your team has WordPress network administration experience
- Your hosting environment supports it properly (not all shared hosts do)
- You have a documented maintenance and rollback strategy
- You've audited plugin compatibility before committing to the architecture
It creates more problems than it solves when:
- Sites have divergent plugin or theme requirements
- Your team treats it like a standard WordPress install
- You're running it on shared hosting without proper object cache support
- You have no staging workflow and no backup testing discipline
The honest answer for most agencies managing client sites: separate installs with centralized management is more resilient and easier to maintain than Multisite. The performance gains of shared infrastructure rarely outweigh the blast radius of network-wide failures. Multisite is a power tool with specific use cases — not a general-purpose multi-site management solution.
What Complex Networks Actually Need
If Multisite is the right call for your situation — or if you're already running one — the maintenance requirements are meaningfully higher than a standard WordPress setup.
You need:
- Automated backups tested for full-network restore (not just file-level backups)
- Object cache properly configured at the server layer
- System-level cron replacing WP-Cron across the network
- Plugin compatibility auditing before any network activation
- A rollback strategy that doesn't depend on manual file restoration under pressure
- Security monitoring that covers REST API endpoints across all subsites
- Database maintenance routines that handle per-site table bloat
This is where a generic maintenance plan fails you. A plan built for a single-site install doesn't account for network-level failure modes, shared table dependencies, or the operational complexity of staging at network scale.
Our Elite WordPress care plan covers complex network environments — including Multisite setups that require network-level backup strategy, cron management, and custom maintenance workflows. If you're evaluating what proper network maintenance looks like, the full service breakdown is here.
For teams still deciding whether to build on Multisite or separate installs, our WordPress maintenance checklist covers the operational requirements that apply regardless of architecture — a useful baseline before you commit to either approach.
The Decision You're Actually Making
Choosing WordPress Multisite isn't a technical decision — it's an operational commitment. You're committing to a shared failure surface, a more complex maintenance model, and infrastructure requirements your hosting setup may not currently meet.
Make that decision with full information. Not because a tutorial made it sound easy, but because you've assessed the maintenance overhead, the rollback complexity, and the plugin ecosystem compatibility for your specific use case.
If you're running a Multisite network and maintenance feels like it's held together with duct tape — or if you're planning one and want to get the architecture right before you're locked in — that's exactly the kind of problem we work through with clients.
Look — I'm writing this because this is a problem I see constantly, and it's also exactly what we built Vimsy to solve. If you want professionals handling this instead of hoping nothing breaks, book a free call.
The complexity of your infrastructure should be matched by the quality of the team maintaining it. Most Multisite networks I've audited are running on maintenance plans designed for single-site installs. That gap is where things eventually break — and the blast radius is every site in your network at once.